Listening First
A backend engineer diving into quantum entropy to lock down his systems. He’s confident with APIs but wants a quick, secure way to level up his encryption without getting buried in docs.
Heads up a financial security team. She knows randomness matters and wants a scalable, compliant solution her developers can pick up fast.
Indie game dev chasing fair, cheat-proof gameplay. He’s on a tight budget and just wants something that works without breaking his flow or the bank
Finding the Gaps
Here’s what we found:
· API keys issued instantly - but no next step
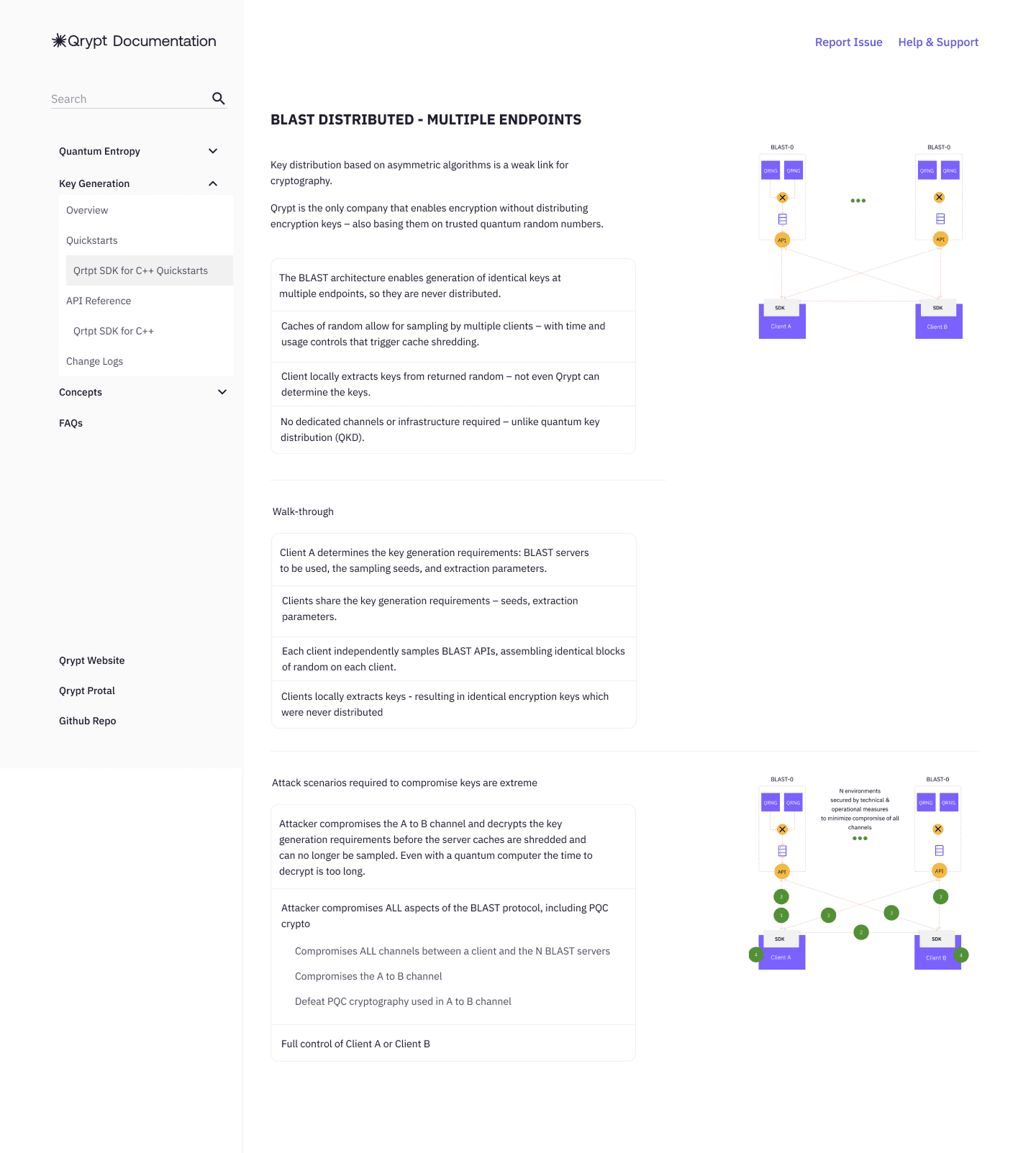
· Docs were thorough - but overwhelming
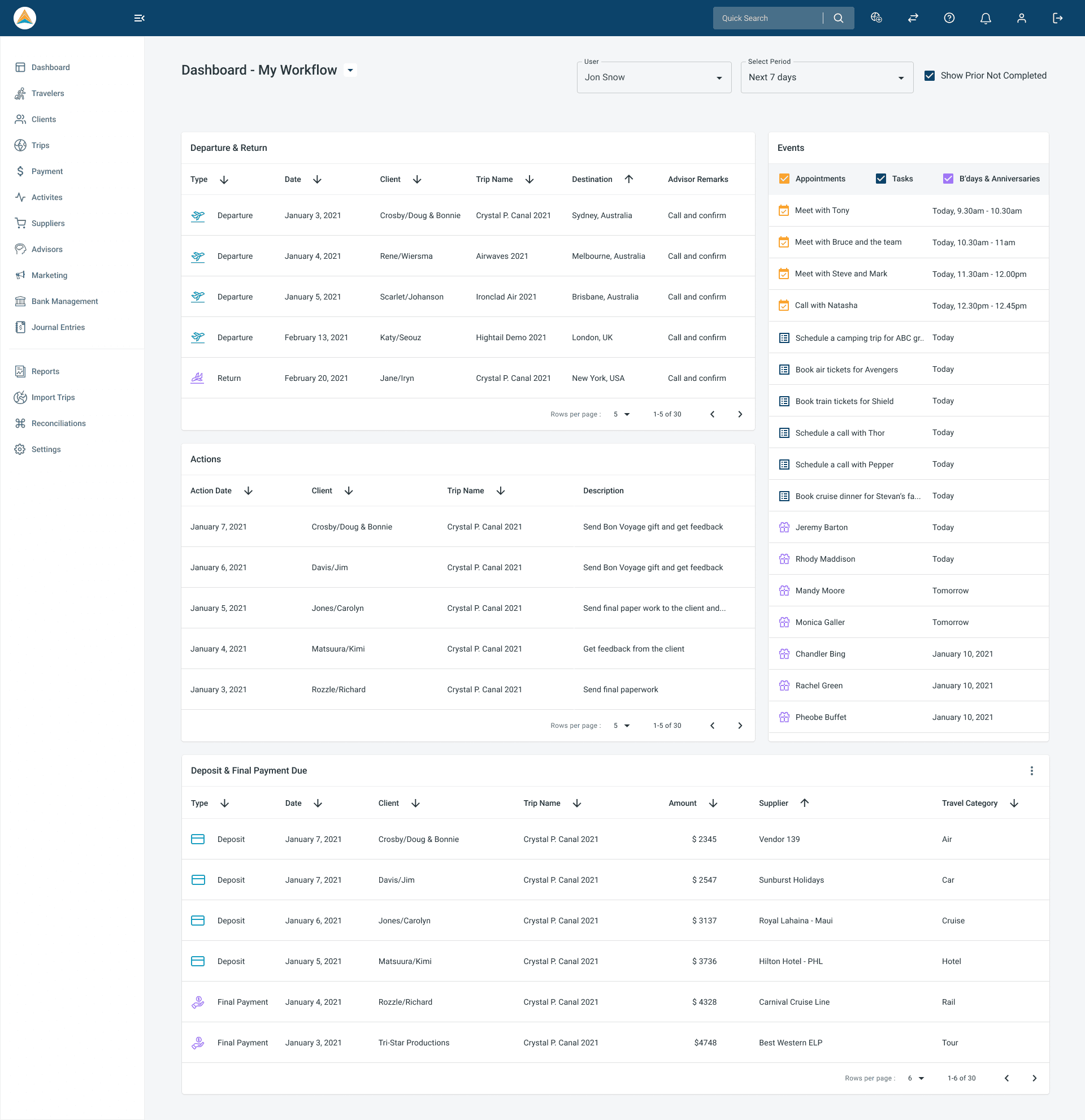
· The dashboard was flexible - but directionless
· No onboarding or use case examples for specific industries
There was friction at the worst moment: right after signup.
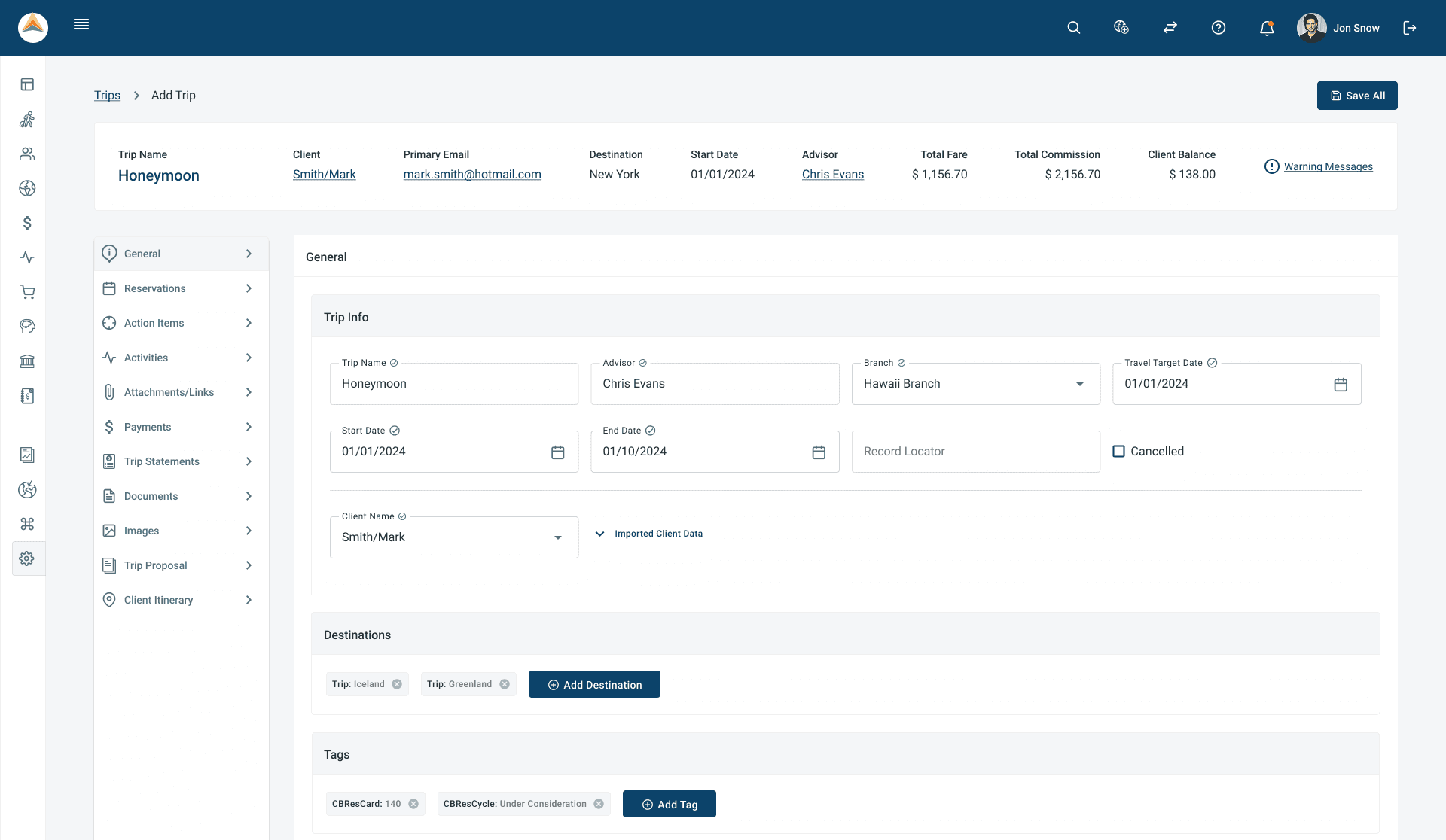
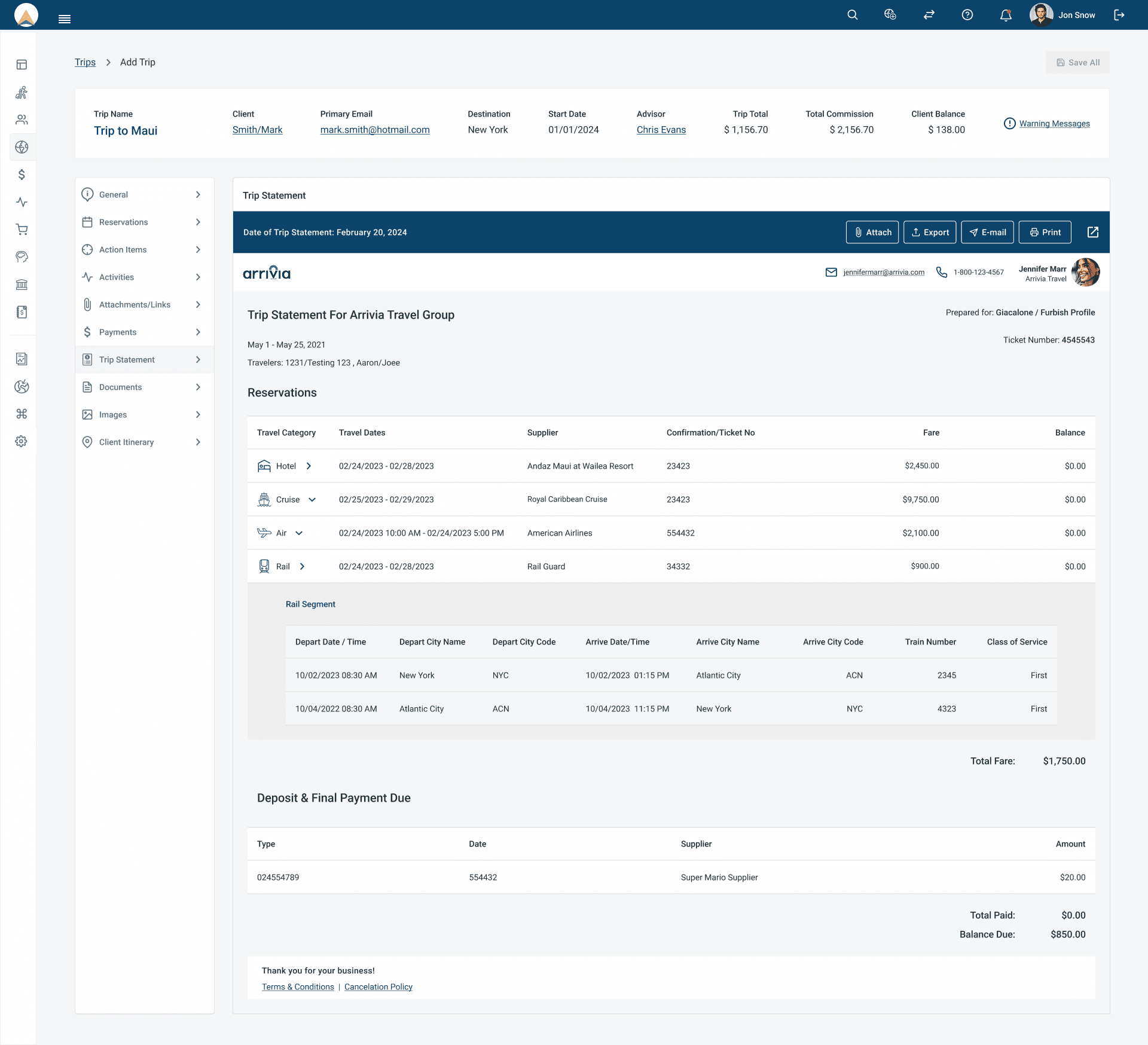
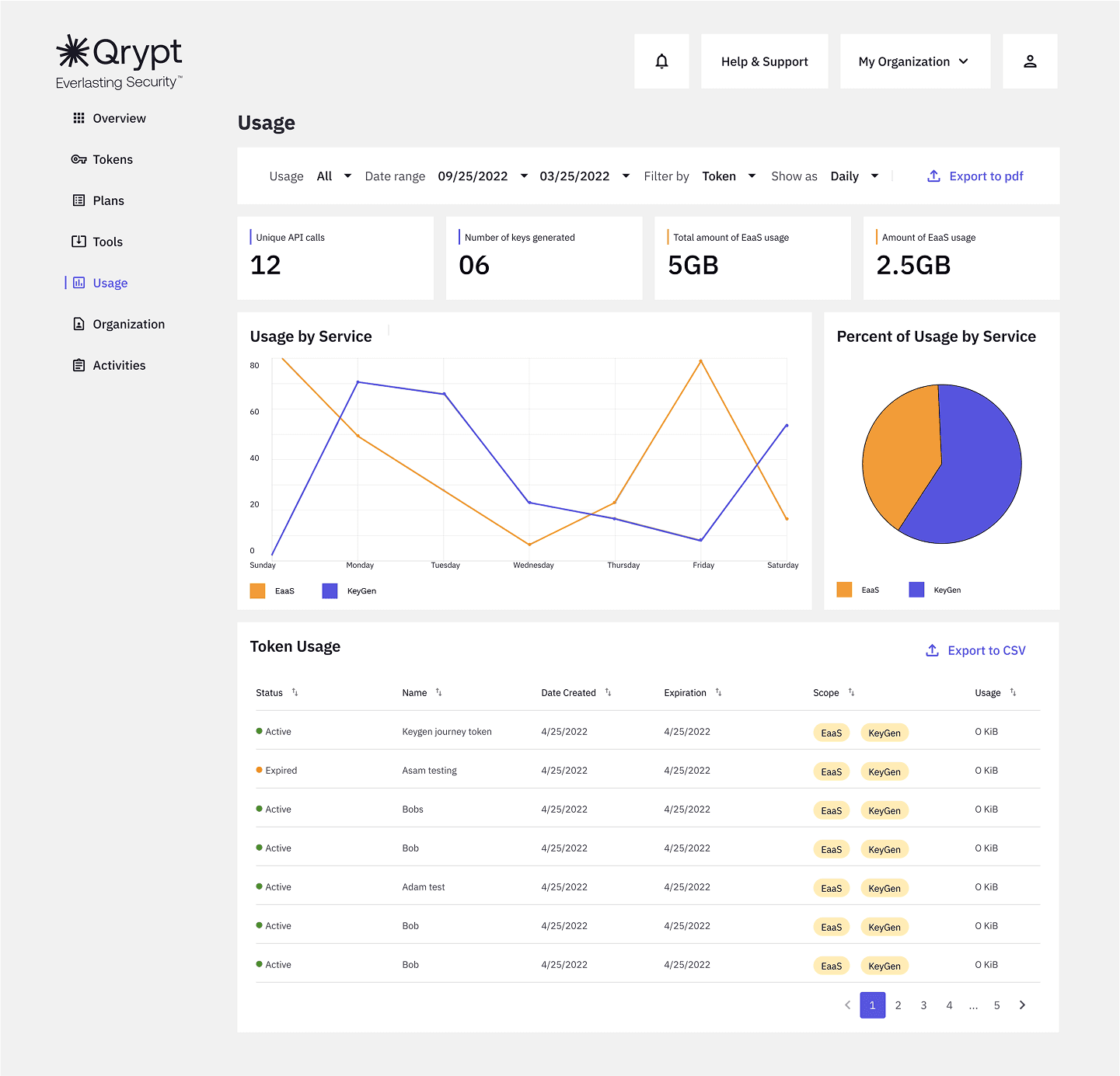
What We Built
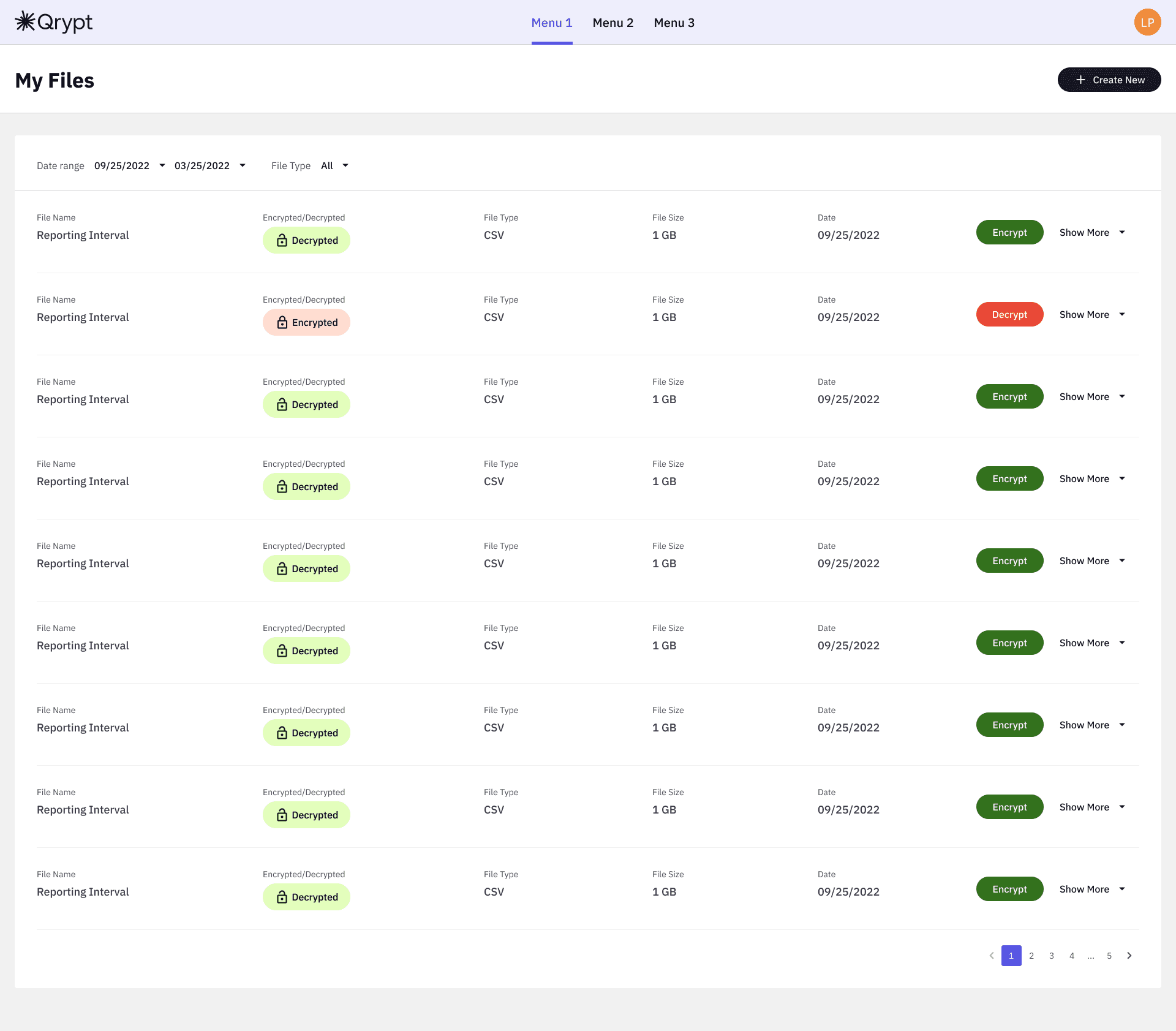
Key changes:
· A “Start Here” onboarding path tailored by role (Developer / Security Architect / Product Owner)
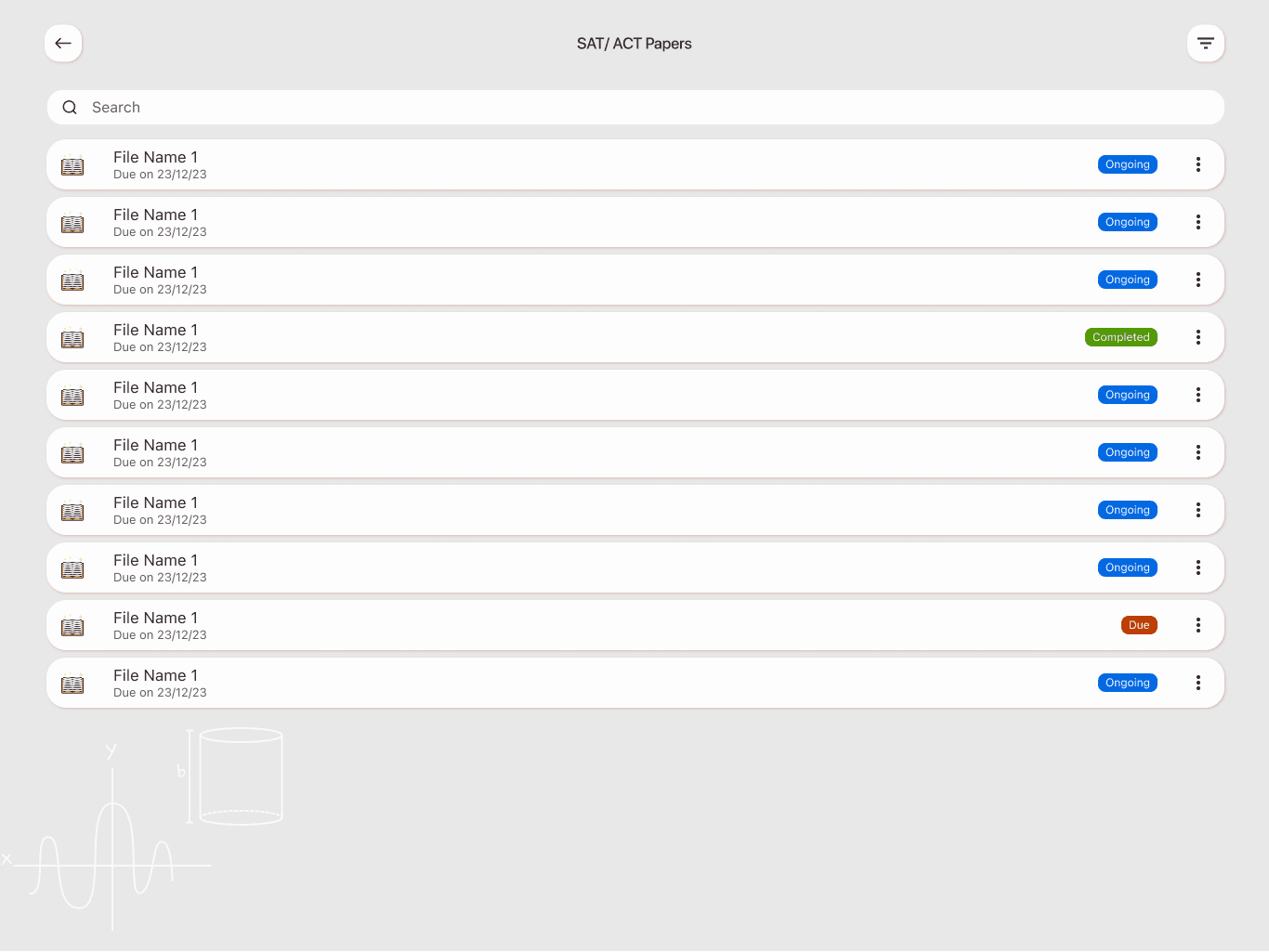
· Use-case templates: “Secure file transfer,” “Keyless encryption,” “IoT randomness”
· Visual indicators for key status and usage rate
· A guided integration flow that teaches by doing
· Improved documentation with embedded code samples and curl commands
Color palettes
Typography
How It Works
What We Learned (and Fixed)
Here’s what we adjusted:
· First-time users skipped docs → So we embedded tutorials directly in the dashboard
· Developers wanted to “test fast” → We built a Postman-ready sandbox
· Industry-specific needs varied → We added role-based onboarding presets
Why It Matters
Qrypt isn’t just a product. It’s the future of encryption. But innovation means nothing if people can’t use it. By putting UX first, we helped developers go from “What is this?” to “I’m already using it.”